Analysis of Top Open Source Firewall Management Tools in 2024
It is crucial for businesses to prioritize robust network security to mitigate the substantial costs associated with data breaches, averaging over $4 million globally, according to cybersecurity statistics. To safeguard the firewall security and integrity of their sensitive data, businesses rely on firewall security management services.
If you are working at an SME or the company is just starting its network security journey without a budget, see open source firewall management tools.
If you are working at an enterprise, explore closed source firewall management software for more comprehensive solutions.
Top 8 open source firewall management software
Table 1. Comparison of top 8 open source firewall management tools
| Tool | GitHub Stars | User Rating* | IPS | IPS Platform | Type | Platform Compatibility |
|---|---|---|---|---|---|---|
| Ansible | 61K | 4.5 out of 211 reviews | ✅ | Snort | Configuration management | Windows, MacOS, Linux |
| Nmap | 9K | 4.7 out of 70 reviews | ❌ | – | Network scanner | Windows, MacOS, Linux |
| CrowdSec | 8K | 4.7 out of 87 reviews | ✅ | CrowdSec | IDS, IPS | Windows, Linux |
| pfSense | 5K | 4.7 out of 289 reviews | ✅ | Snort | firewall | Windows, MacOS |
| OSSEC | 4K | 4.6 out of 10 reviews | ✅ | OSSEC | IDS | Windows, MacOS, Linux |
| Snort | 2K | 4.1 out of 27 reviews | ✅ | Snort | IDS, IPS | Windows, Linux |
| IPFire(Netfilter) | less than 1K | – | ✅ | Suricata | firewall | Windows, Linux |
| OPNsense | less than 1K | – | ✅ | Suricata | firewall | MacOS |
*Based on data from B2B review platforms
You may explore details regarding
in the following sections.
Disclaimer: ❌ means that the AIMultiple team couldn’t identify public evidence about a specific feature.
Inclusion criteria:
- Each vendor listed in the table provides intrusion detection and open source firewall management services in addition to other cyber security solutions. An intrusion detection system (IDS) is a critical component of firewall tools, enabling the detection of unauthorized network access, security breaches, and suspicious activities within the network infrastructure. It is a vital component for detecting and alerting potential security threats.
- The ranking is determined by the GitHub stars.
1. Ansible
Ansible, with its extensive GitHub stars and user acclaim for configuration management, plays a vital role in firewall security management. Although primarily known for configuration management, Ansible integrates seamlessly with Snort for IPS capabilities, ensuring proper firewall configurations and efficient network security policy management of firewalls across Windows, MacOS, and Linux platforms.
Figure 1. Shows how Ansible security policy management software works
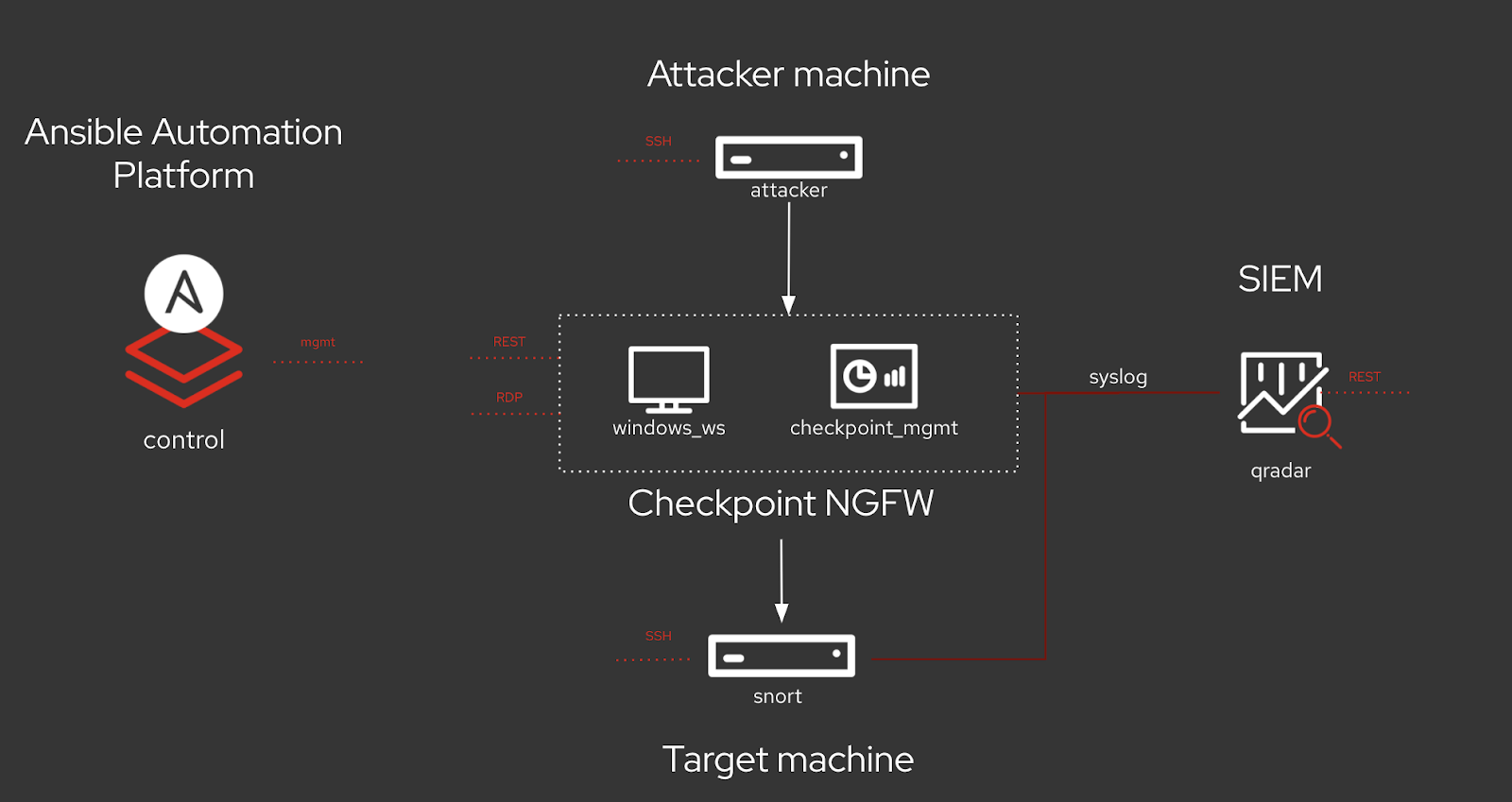
Source: Ansible2
2. NMap
Nmap, renowned for its network scanning capabilities, lacks IPS functionalities but remains a crucial tool for network security assessments. It aids in identifying potential security threats, performing regular security audits, and optimizing firewall rulesets for a secure network environment across Windows, MacOS, and Linux systems.
3. CrowdSec
CrowdSec, functioning as both an intrusion detection system (IDS) and intrusion prevention system (IPS), offers robust protection against cyber threats. It specializes in managing firewall policies and rules, optimizing firewall rulesets, and ensuring effective threat management. Its compatibility with Windows and Linux platforms makes it a versatile choice for organizations prioritizing network security.
Figure 1. Shows how CrowdSec firewall management system works
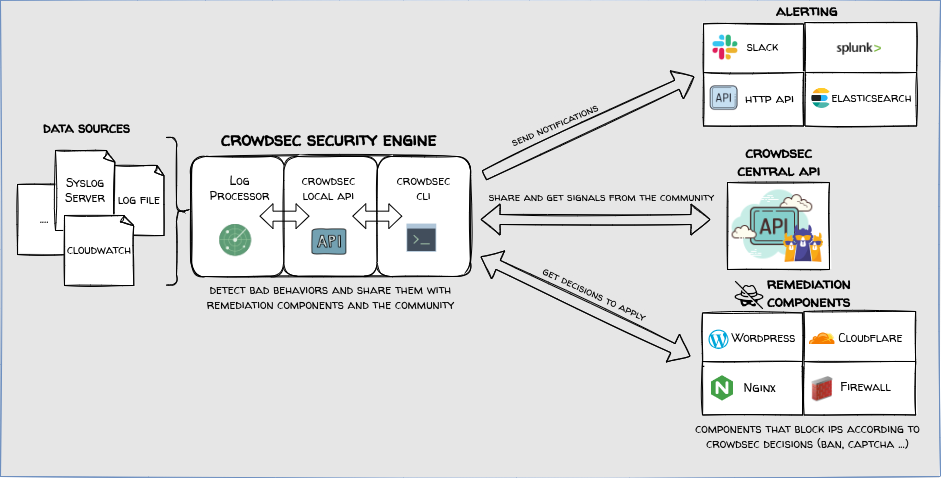
Source: CrowdSec3
4. Pfsense
With a solid user rating and GitHub stars, pfSense is a popular choice for firewall management. It boasts compatibility with Windows and MacOS, making it accessible to a wide range of users. Its permissive license and support for the Snort IPS platform contribute to its effectiveness in network security.
5. OSSEC
OSSEC, known for its host-based intrusion detection system (HIDS), provides comprehensive security by managing firewall rules and policy optimization and conducting regular network security audits. Its support for Windows, MacOS, and Linux platforms ensures a secure network environment across diverse IT infrastructures.
6. Snort
Snort, a widely recognized open source IDS/IPS tool, excels in intrusion detection and prevention capabilities. With strong GitHub stars and user ratings, Snort enhances firewall security through proactive threat management, deep packet inspection, and effective firewall rule management across Windows and Linux systems.
7. IPFire (Netfilter)
IPFire is a secure firewall management center. It, powered by the Netfilter firewall software, prioritizes strong protection and network security. It offers capabilities for managing firewall policies and rules, optimizing firewall rulesets, and conducting regular firewall security audits. Its compatibility with Windows and Linux platforms makes it a versatile choice for organizations seeking comprehensive security solutions.
8. OPNsense
OPNsense, despite its limited GitHub presence, offers valuable firewall management features and compatibility with Suricata for IPS functionalities on MacOS.
Figure 2. Shows how to enable IPS functionalities on OPNsense firewall management software
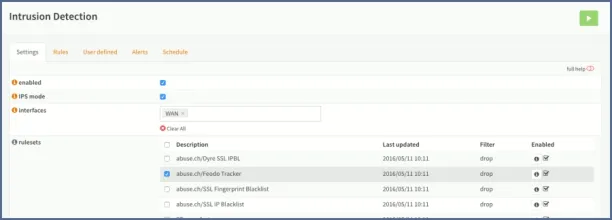
Source: OPNsense4
It simplifies firewall management tasks, allowing network administrators to implement effective firewall rule administration and optimize firewall configurations for enhanced security and network performance.
Figure 3. shows OPNsense firewall management software’s dashboard
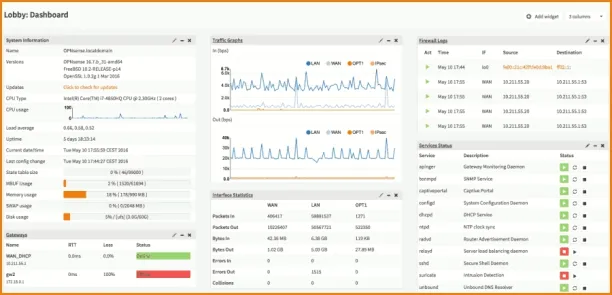
Source: OPNsense5
Exploring open source firewall management tools
At the core of open source firewall management software is the focus on network security. These tools empower network administrators and security teams to configure firewall rules, manage network traffic, and conduct regular security audits to detect and mitigate potential threats effectively. Open source firewall management software offers a cost-effective solution, providing robust security features without the high licensing fees associated with proprietary solutions.
Key features for selecting the right firewall software
1. Intrusion prevention system
An IPS goes beyond detection by actively preventing potential threats and malicious activities, enhancing overall network security. It blocks suspicious activities identified by the IDS.
Figure 4. Shows the differences between IDS and IPS
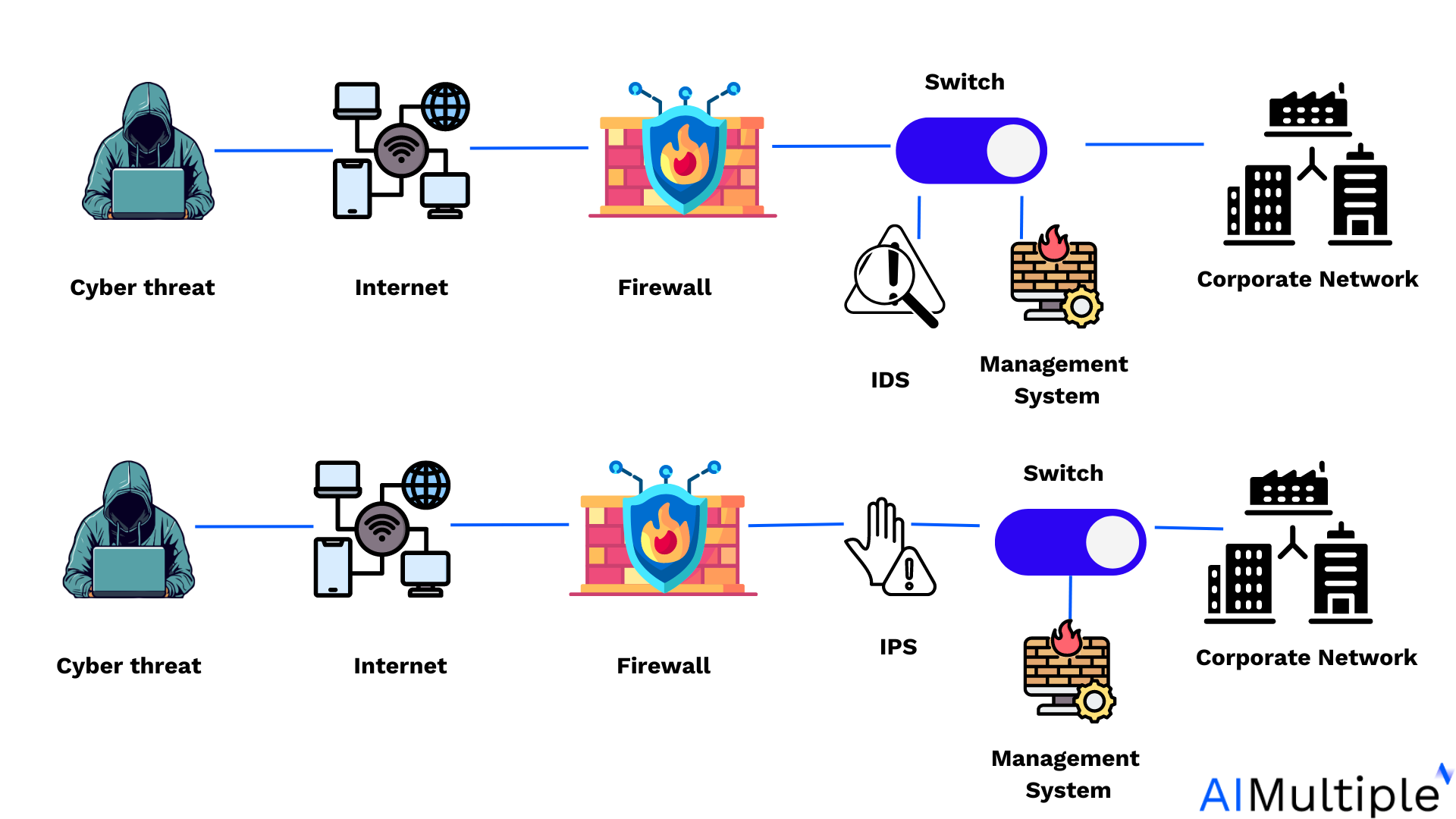
Source: Wallarm6
IDS detect potential threats and alert administrators, while IPS actively prevent cyber attacks by taking appropriate action upon detection.
2. IPS platform
The IPS platform is the foundation for effective threat prevention and mitigation, supporting robust security policies and real-time threat response.
CrowdSec: It uses a community-driven approach, where authorized users contribute and share detection rules based on real-time threat intelligence and collective security incidents7. CrowdSec emphasizes crowd-sourced threat intelligence and behavioral analysis to detect and block malicious activities effectively.
Snort: Snort utilizes a signature-based rule set, where predefined signatures are used to identify known threats based on patterns and behaviors. It primarily focuses on real-time packet inspection and signature-based detection to identify and block malicious network traffic.
OSSEC: It employs a combination of signature-based rules, anomaly detection, and log analysis to detect and respond to security events. OSSEC focuses on host-based intrusion detection (HIDS), monitoring system logs, file integrity checking, and rootkit detection.
Suricata: Suricata features a multi-threaded rule engine with support for signature-based rules, protocol analysis, and emerging threat detection. It emphasizes high-speed security and traffic analysis, protocol analysis, and the detection of complex threats like zero-day exploits and evasion techniques.
3. Firewall management type
Configuration management: Businesses choose this type of firewall management solution for efficient management and optimization of firewall configurations, ensuring security policies are accurately enforced.
Network scanner: Selected for its capability to scan and identify vulnerabilities within the network, aiding in proactive threat detection and prevention.
Intrusion detection system (IDS): Intrusion detection systems are favored for their ability to detect and alert on suspicious activities within the network, enhancing threat detection capabilities.
Intrusion detection system (IPS): Intrusion prevention systems are selected to actively block identified security breaches, providing an added layer of defense against malicious activities.
Firewall: Firewall solutions are fundamental for businesses to establish secure boundaries, control inbound and outbound traffic, and enforce security policies to protect sensitive data and resources.
4. Platform compatibility
Ensuring open source firewall management software are compatible with the organization’s IT infrastructure, including Windows, MacOS, Linux, and network devices, is essential for seamless integration and effective firewall security management.
8 Benefits of open source firewall management solutions
1. Cost effectiveness and community support
Open source firewall security management software provides cost-effective solutions by offering robust security features without the high licensing fees of proprietary software. Additionally, they often benefit from a collaborative community that continuously improves and updates the software, ensuring enhanced security and functionality over time.
2.Network security reinforcement
Open source firewall management software empower security administrators and security teams to strengthen network security by implementing effective firewall rules and security policies. These tools enable the management of traditional firewalls and next-generation firewalls, ensuring comprehensive protection against cyber threats.
3.Efficient firewall management
Proper firewall management is essential for regulating network traffic, optimizing firewall rulesets, and conducting regular security audits. Open source firewall management solutions provide a centralized platform for managing firewalls across an organization’s network, allowing for efficient configuration changes and threat management.
4.Robust security firewall policies
With open source security management software, organizations can define and enforce robust security firewall policy tailored to their specific needs. These tools facilitate the creation of next-generation firewalls policies, incorporating features like deep packet inspection, intrusion prevention, and stateful firewalls to combat advanced threats effectively.
5.Comprehensive threat detection
Intrusion detection systems (IDS) and intrusion prevention systems (IPS) are vital components of open source firewall security management software, enabling the detection and prevention of unauthorized network access and malicious activities. These tools utilize deep packet inspection and threat management techniques to identify and block suspicious network traffic.
6.Centralized management and reporting
Open source firewall management solutions offer centralized management capabilities, allowing security administrators to monitor firewall changes, analyze firewall logs, and generate compliance reports. This centralized approach streamlines firewall management tasks and ensures network security policy management and regulatory requirements.
7.Optimized firewall configurations
Effective firewall management involves optimizing firewall performance and configurations to mitigate firewall security risks and prevent data breaches. Open source firewall management tools provide graphical user interfaces (GUIs) for configuring firewall rules, resolving conflicting configurations, and managing virtual appliances like proxy firewalls and web proxies.
8.Secure network connectivity
Open source firewall management tools automate firewall rule administration to help organizations secure network connectivity, authorize legitimate users, and block unauthorized access attempts. These tools facilitate the implementation of global rules, packet filtering, and destination IP address restrictions to safeguard network resources.
Further reading
- Firewall Integration of Top Management Services in 2024
- Firewall Audit Logs: Analysis and 6 Steps for Improvement in 2024
- Top 7 Open Source Firewall Audit Tools in 2024: Analysis & Comparison
FAQs
What is a management firewall?
A management firewall refers to a specialized type of firewall that is specifically configured and dedicated to managing network traffic related to administrative tasks, such as accessing network management interfaces, remote administration, and continuous compliance. It helps secure these critical network management functions by controlling access and ensuring that only authorized personnel can make changes or access sensitive network components.
What does a firewall manager do?
A firewall manager is responsible for overseeing the configuration, compliance standards, deployment, monitoring, and maintenance of firewall systems within an organization’s network. Overall, a firewall manager plays a critical role in safeguarding network infrastructure, preventing cyber threats, and maintaining a secure network environment.
External Links
- 1. Red Hat Ansible Security Automation Guide. Ansible. Accessed: 25/April/2024.
- 2. CrowdSec Security Engine Documentation. CrowdSec. Accessed: 25/April/2024.
- 3. OPNsense Markets & Features. OPNsense. Accessed: 25/April/2024.
- 4. OPNsense Markets & Features. OPNsense. Accessed: 25/April/2024.
- 5. Intrusion Prevention system. Wallarm. Accessed: 25/April/2024.
- 6. CrowdSec. CrowdSec. Accessed: 25/April/2024.

Cem is the principal analyst at AIMultiple since 2017. AIMultiple informs hundreds of thousands of businesses (as per Similarweb) including 60% of Fortune 500 every month.
Cem's work has been cited by leading global publications including Business Insider, Forbes, Washington Post, global firms like Deloitte, HPE, NGOs like World Economic Forum and supranational organizations like European Commission. You can see more reputable companies and media that referenced AIMultiple.
Throughout his career, Cem served as a tech consultant, tech buyer and tech entrepreneur. He advised enterprises on their technology decisions at McKinsey & Company and Altman Solon for more than a decade. He also published a McKinsey report on digitalization.
He led technology strategy and procurement of a telco while reporting to the CEO. He has also led commercial growth of deep tech company Hypatos that reached a 7 digit annual recurring revenue and a 9 digit valuation from 0 within 2 years. Cem's work in Hypatos was covered by leading technology publications like TechCrunch and Business Insider.
Cem regularly speaks at international technology conferences. He graduated from Bogazici University as a computer engineer and holds an MBA from Columbia Business School.
Sources:
AIMultiple.com Traffic Analytics, Ranking & Audience, Similarweb.
Why Microsoft, IBM, and Google Are Ramping up Efforts on AI Ethics, Business Insider.
Microsoft invests $1 billion in OpenAI to pursue artificial intelligence that’s smarter than we are, Washington Post.
Data management barriers to AI success, Deloitte.
Empowering AI Leadership: AI C-Suite Toolkit, World Economic Forum.
Science, Research and Innovation Performance of the EU, European Commission.
Public-sector digitization: The trillion-dollar challenge, McKinsey & Company.
Hypatos gets $11.8M for a deep learning approach to document processing, TechCrunch.
We got an exclusive look at the pitch deck AI startup Hypatos used to raise $11 million, Business Insider.
To stay up-to-date on B2B tech & accelerate your enterprise:
Follow on

Comments
Your email address will not be published. All fields are required.